Best Email Security Services in Dubai, UAE: Your 2026 Complete Guide
Email security is essential for businesses in the UAE because email remains the main communication channel and one of the most common entry points for cyber attacks. Every morning in Dubai, business owners just like you check their email first thing. It's where deals are made, clients are contacted, and daily operations are coordinated. But what if I told you that this essential tool could also be your biggest security risk?
Here at Al Hutaib, we've helped hundreds of UAE businesses secure their email communications over the past decade. We've seen firsthand how a single phishing email can disrupt operations for weeks, and how proper email security solutions can transform a company's digital resilience. This guide isn't just another technical article—it's a practical roadmap based on real experience protecting businesses across Dubai, Abu Dhabi, and Sharjah.
Quick Email Security Insight from Our Experience:
UAE businesses receive 3 times more phishing attempts than the global average. The good news? With the right email security measures, you can block 99.9% of these threats automatically.
What You'll Learn From Our Guide
- ✓ Understanding the real email threats facing UAE businesses today
- ✓ Key features every email security solution must have
- ✓ Detailed analysis of top email security solutions available
- ✓ How to choose the right solution for your specific needs
- ✓ Implementation best practices for maximum protection
Understanding Email Security Threats in Today's UAE Business Environment
Let's start with the reality we see every day in our work with UAE companies. Email threats have evolved far beyond simple spam. They're now sophisticated, targeted, and increasingly difficult to detect without proper protection.
Business Email Compromise: The Silent Threat
BEC attacks don't use malware or suspicious links. Instead, they impersonate CEOs or managers requesting urgent wire transfers. We helped a Dubai trading company recover from a BEC attack that almost cost them AED 450,000. The email looked completely legitimate—same tone, same signature, same everything.
Phishing: More Personal Than Ever
Modern phishing emails reference real events, use local UAE references, and often come from seemingly legitimate UAE domains. They're not just generic "Nigerian prince" emails anymore. They're tailored to your industry, your location, and sometimes even your specific role in the company.
Why UAE Businesses Are Particularly Vulnerable
Through our work across the Emirates, we've identified three key factors that make local businesses attractive targets:
International Business Focus
Regular international transactions and communications create more entry points for attackers pretending to be overseas partners or clients.
Compliance Requirements
The UAE Data Protection Law and NESA standards mean businesses must demonstrate robust security measures. Attackers know pressure to comply can lead to rushed decisions.
Rapid Digital Transformation
As businesses quickly adopt cloud services and remote work, security sometimes lags behind implementation, creating vulnerabilities.
Essential Features Every Email Security Services Needs in 2026
Based on our experience implementing email security for UAE businesses, here are the non-negotiable features that actually make a difference in real-world scenarios:
Real-time AI Threat Detection
Traditional signature-based detection can't keep up. Look for solutions that use artificial intelligence to analyze email patterns, sender behavior, and content context in real time. This catches zero-day attacks that haven't been seen before.
Why this matters: Catches evolving threats that traditional solutions miss
Business Email Compromise Protection
Specific detection for impersonation attempts, analyzing email headers, sender patterns, and request context. Should flag unusual payment requests or sensitive information sharing.
Why this matters: Prevents financial loss from impersonation attacks
Email Encryption That Actually Works
Not just any encryption—look for solutions that make it easy for recipients to read encrypted emails without complicated steps. The best solutions work transparently for both sender and receiver.
Why this matters: Ensures compliance with UAE data protection requirements
UAE-Specific Compliance Features
Built-in templates and reporting for UAE Data Protection Law and NESA compliance. Should include data residency options and Arabic language support for policies and alerts.
Why this matters: Simplifies regulatory compliance for local businesses
Detailed Analysis: Top Email Security Service Solutions for UAE Businesses
Let's examine specific solutions we've implemented across UAE businesses, with honest assessments based on real deployment experience. Each solution has different strengths that make it suitable for particular business scenarios in Dubai, Abu Dhabi, and the wider Emirates.
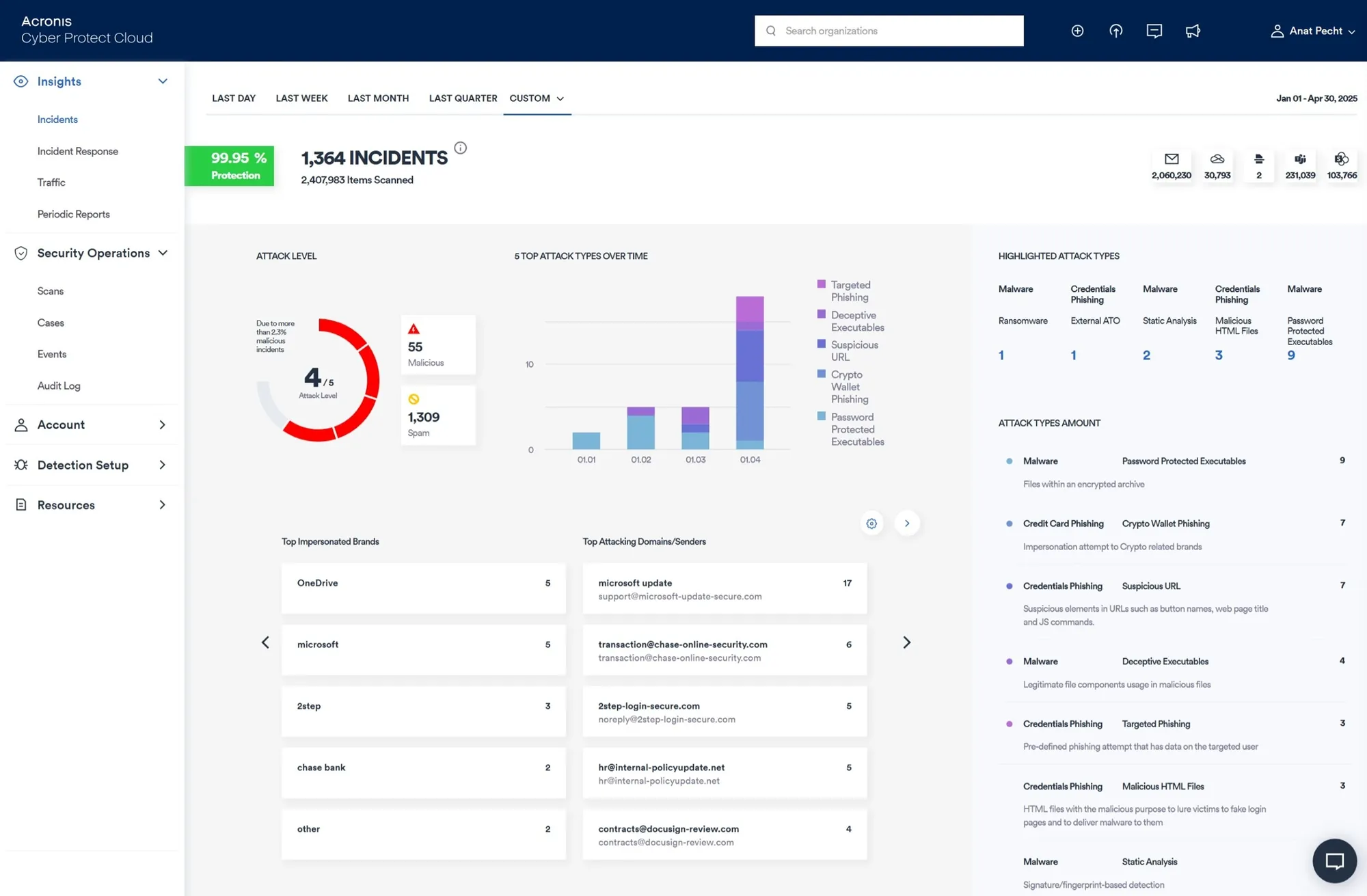
Acronis Email Security
AI-Powered Cyber Protection with Real-Time Threat Detection
AI-Powered Threat Detection
Machine learning algorithms analyze email patterns and content in real-time, catching zero-day attacks and sophisticated phishing attempts that traditional solutions miss.
Lightning-Fast Deployment
Cloud-native architecture means protection can be activated in hours, not days. No MX record changes required for Microsoft 365 environments.
Advanced BEC Protection
Specifically designed to catch Business Email Compromise attempts through behavioral analysis and sender verification.
What We Like (From UAE Implementation Experience)
- ✓ Real-time AI detection that adapts to UAE-specific threat patterns
- ✓ Seamless integration with Microsoft 365 and Google Workspace
- ✓ Minimal false positives for Arabic/English bilingual emails
- ✓ Excellent for businesses with remote teams across UAE and internationally
Ideal UAE Business Scenarios
Perfect for UAE businesses that:
-
🏢Have mixed IT environments with cloud and on-premise components
-
🌐Need quick implementation without business disruption
-
📧Require advanced protection without dedicated security staff
Technical Specifications & UAE Compliance
Supported Platforms
- • Microsoft 365 (API-based integration)
- • Google Workspace
- • On-premise Exchange Servers
- • Other SMTP-based systems
UAE Compliance Features
- ✓ Data encryption meeting UAE standards
- ✓ Audit logging for compliance reporting
- ✓ Data residency options available
FortiMail by Fortinet
Enterprise-Grade Email Security with Advanced Threat Protection
Enterprise Scalability
Designed for large organizations with complex email infrastructures, supporting high-volume email traffic with minimal performance impact.
Advanced DLP Capabilities
Comprehensive Data Loss Prevention with predefined policies for UAE compliance requirements and custom rule creation.
Security Fabric Integration
Seamless integration with Fortinet's Security Fabric for unified threat intelligence and coordinated response across network, endpoint, and cloud.
Key Advantages for UAE Enterprises
- ✓ Flexible deployment options (appliance, virtual, cloud)
- ✓ Advanced sandboxing for zero-day threat detection
- ✓ Comprehensive reporting for compliance audits
- ✓ High availability configurations for critical business operations
Considerations for Implementation
Best suited when:
-
👨💼Dedicated IT security team available for management
-
🏗️Already using Fortinet security products
-
⚖️Require granular control and custom policies
Deployment Options for UAE Businesses
Cloud-Based
Managed service with rapid deployment, ideal for businesses without dedicated infrastructure teams.
Virtual Appliance
Flexible deployment on existing virtualization platforms, good for organizations with VMware or Hyper-V environments.
Physical Appliance
Dedicated hardware for maximum performance, suitable for large enterprises with high email volumes.
Microsoft 365 Defender
Native Email Protection for Microsoft 365 Environments
Built-in Advantages
- ✓ Native integration with Microsoft 365 ecosystem
- ✓ Unified security management through Microsoft Defender portal
- ✓ Automatic updates and maintenance by Microsoft
- ✓ Seamless integration with Azure Active Directory
Considerations for UAE Businesses
-
💡Best as foundational protection
Often needs additional layers for comprehensive security
-
🔒Requires proper configuration
Default settings may not provide optimal protection
Quick Comparison: Email Security Solutions for UAE
| Feature | Acronis Email Security | FortiMail | Microsoft 365 Defender |
|---|---|---|---|
| Deployment Speed |
✓✓✓
Very Fast (Hours)
|
✓✓
Moderate (Days)
|
✓✓✓
Instant (If already using M365)
|
| AI Threat Detection |
✓✓✓
Advanced AI/ML
|
✓✓
Machine Learning
|
✓
Basic AI
|
| UAE Compliance Support |
✓✓✓
Built-in templates
|
✓✓✓
Customizable policies
|
✓✓
Basic compliance
|
| Management Complexity |
✓✓✓
Low (User-friendly)
|
✓
High (Expert required)
|
✓✓
Medium (IT knowledge needed)
|
| Best For UAE Business Size | SMB to Enterprise | Medium to Large | SMB |
Note: The "best" solution depends on your specific business needs, existing infrastructure, and security requirements. Many UAE businesses use a layered approach with multiple solutions.
Hybrid Approach: Layered Email Security for Maximum Protection
Many successful UAE businesses use a combination of solutions for defense-in-depth protection. Here's a common effective strategy we recommend:
Foundation Layer
Microsoft 365 Defender or built-in platform security for basic protection
Advanced Layer
Specialized solution like Acronis for AI threat detection and BEC protection
Compliance Layer
DLP and encryption solutions for regulatory requirements
Our Recommendation: Start with what you need today, but choose solutions that can grow with your business. The UAE business environment evolves quickly, and your email security should be able to adapt to new threats and compliance requirements.
Detailed Breakdown: Most Common Email Threats Targeting UAE Businesses
Knowing what you're up against is the first step in building proper defense. Here's a closer look at the specific threats we encounter most frequently while protecting businesses across Dubai, Abu Dhabi, and Sharjah.
Phishing Attacks
The most prevalent threat in UAE business emails
How It Works
Attackers send emails that appear to come from legitimate sources like banks, government entities, or trusted suppliers. These emails create urgency, prompting recipients to click links or provide sensitive information.
UAE-Specific Example: Emails pretending to be from UAE Central Bank, DED, or local telecom providers requesting immediate account verification.
Why It's Effective Here
- • High volume of official-looking government communications
- • Multilingual workforce with varying security awareness
- • Rapid business pace leads to rushed decisions
Business Email Compromise (BEC)
Sophisticated attacks targeting financial transactions
Attack Method
Cybercriminals study organizational structures, then impersonate executives or trusted partners to authorize fraudulent payments. These emails don't contain malware—they rely on social engineering.
Common in UAE: Impersonation of CEOs requesting urgent wire transfers to "new suppliers" or "overseas partners."
Why UAE Businesses Are Targets
- • High-value international transactions common
- • Hierarchical business structures with clear authority lines
- • Time zone differences with international partners create communication gaps
Malware & Ransomware Delivery
Destructive payloads hidden in seemingly innocent emails
How It Spreads
Malicious attachments or links install software that can encrypt files (ransomware), steal data (spyware), or create backdoors for future attacks. These often come disguised as invoices, shipment notifications, or resume files.
Local Variation: Ransomware emails referencing local events like GITEX, Dubai Shopping Festival, or Expo-related opportunities.
Business Impact in UAE
- • Critical business downtime during high-revenue periods
- • Compliance violations with UAE data protection regulations
- • Reputation damage in tight-knit business communities
Email Spoofing
Forged sender addresses undermining trust in communication
The Technical Trick
Attackers manipulate email headers to make messages appear from legitimate sources. Recipients see familiar sender names and addresses, making them more likely to trust the content.
Common Targets: Spoofed emails from local government agencies, banks, or known business partners requesting sensitive information.
Detection Challenges
- • Traditional spam filters often miss sophisticated spoofing
- • Employees trust familiar sender names without verification
- • DMARC implementation varies across UAE organizations
Tangible Benefits: What Proper Email Security Actually Delivers for UAE Businesses
Beyond just stopping threats, effective email security solutions deliver measurable benefits that impact your bottom line, compliance status, and business reputation. Here's what you can realistically expect when implementing the right protection.
Direct Financial Protection
-
✓
Prevent Financial Fraud
Stop BEC attacks that target payment authorizations and invoice manipulations
-
✓
Avoid Ransom Payments
Block ransomware before it encrypts critical business data
-
✓
Reduce Recovery Costs
Minimize expenses associated with incident response and data restoration
Compliance & Legal Protection
-
✓
Meet UAE Regulations
Satisfy requirements under UAE Data Protection Law and NESA standards
-
✓
Audit Trail Creation
Maintain detailed logs for compliance reporting and legal requirements
-
✓
Data Residency Control
Ensure sensitive data remains within UAE jurisdiction as required
Business Continuity & Productivity
-
✓
Minimize Downtime
Prevent email-borne attacks that disrupt critical business operations
-
✓
Reduce IT Burden
Automated protection decreases manual security monitoring workload
-
✓
Clean Inbox Management
Eliminate spam and malicious emails that waste employee time
Reputation & Trust Preservation
-
✓
Protect Client Trust
Prevent compromised emails that damage relationships with partners and customers
-
✓
Avoid Public Breaches
Stop data leaks that could lead to negative publicity and brand damage
-
✓
Strengthen Partner Confidence
Demonstrate security maturity to international business partners
How These Benefits Translate to Daily Operations
Operational Efficiency
Employees spend less time dealing with spam and security incidents, focusing on productive work instead.
Risk Management
Clear visibility into email threats allows proactive security management rather than reactive firefighting.
Business Growth
Strong security posture enables pursuit of larger contracts and partnerships with stringent security requirements.
Navigating UAE Compliance Requirements for Email Security
For businesses operating in the UAE, email security isn't just about protection—it's about compliance. Understanding and meeting local regulatory requirements is essential for avoiding penalties and maintaining business operations. Here's what you need to know.
Key UAE Regulations Impacting Email Security
UAE Data Protection Law
- • Requires protection of personal data in electronic communications
- • Mandates breach notification within strict timeframes
- • Specifies data retention and deletion requirements
Email Security Connection: Email encryption, access controls, and audit logging are essential for compliance.
NESA Standards
- • Sets baseline security requirements for UAE entities
- • Mandates specific technical controls for email systems
- • Requires regular security assessments and monitoring
Email Security Connection: Advanced threat protection, DMARC implementation, and security monitoring are required.
Email Security Compliance Checklist for UAE Businesses
Email Encryption Implementation
Ensure sensitive data in emails is encrypted in transit and at rest, especially for communications containing personal information.
Access Control & Authentication
Implement strong authentication mechanisms and role-based access controls for email systems.
DMARC, DKIM, SPF Configuration
Properly configure email authentication protocols to prevent spoofing and demonstrate security maturity.
Audit Logging & Monitoring
Maintain comprehensive logs of email access, modifications, and security events for compliance reporting.
Data Residency Considerations
Ensure email data storage and processing comply with UAE data sovereignty requirements.
Remember that compliance isn't a one-time checkbox exercise. Regular reviews and updates are necessary as both threats and regulations evolve. Working with a local partner who understands UAE compliance requirements can simplify this process significantly.
How Email Security Integrates with Your Overall UAE Business Security Strategy
Email security doesn't exist in isolation. For maximum protection, it needs to work seamlessly with your other security measures. Here's how proper email security integrates with the broader security ecosystem that UAE businesses should maintain.
The Security Ecosystem Approach
Think of email security as one essential layer in a multi-layered defense strategy. When all layers work together, they create a security posture that's much stronger than the sum of its parts.
Complementary Security Measures
-
🖥️Endpoint Protection
Catches threats that bypass email filters but reach user devices
-
🌐Network Security
Monitors for malicious traffic patterns from compromised accounts
-
☁️Cloud Security
Protects cloud email platforms and integrated applications
Integration Benefits
- ✓ Shared threat intelligence across security layers
- ✓ Unified monitoring and incident response
- ✓ Reduced management complexity through integrated consoles
- ✓ Comprehensive compliance reporting from single platform
Integration with Backup Solutions
Email Data Protection
Regular backups of email data ensure recovery from ransomware or accidental deletion. Learn more about our Microsoft 365 backup solutions.
Compliance Archiving
Integrated archiving solutions maintain email records for regulatory requirements while security solutions protect active communications.
Integration with User Training
Security Awareness Programs
Technology alone isn't enough. Regular training helps users recognize threats that might bypass technical controls.
Phishing Simulation
Simulated phishing campaigns combined with email security metrics show where additional training is needed.
Practical Integration Strategy
Start with Core Email Security
Implement basic email protection first—anti-malware, anti-spam, and basic filtering. This gives immediate protection while you plan integration.
Identify Integration Points
Look at your existing security tools. Which ones can share information with your email security solution? Start with those integrations first.
Implement Unified Monitoring
Create a single dashboard or reporting system that shows threats across email, network, and endpoints. This gives complete visibility.
Regular Review & Adjustment
Security needs evolve. Regular reviews ensure all components continue working together effectively as threats and business needs change.
Email Security Quick Reference Guide for UAE Businesses
Solution Selection Quick Guide
| Business Size | Primary Needs | Recommended Focus | Implementation Priority |
|---|---|---|---|
| Small Business (1-50 employees) | Basic protection, ease of use, cost-effectiveness | Cloud-based solutions with automated management | 1. Basic filtering 2. Anti-phishing 3. Simple encryption |
| Medium Enterprise (51-250 employees) | Advanced protection, compliance, integration | Comprehensive platforms with local support | 1. AI threat detection 2. Compliance features 3. Integration capabilities |
| Large Corporation (250+ employees) | Enterprise-grade, customization, advanced features | Enterprise solutions with dedicated support | 1. Custom policies 2. Advanced DLP 3. Full integration |
Common Configuration Mistakes to Avoid
Overly Aggressive Filtering
Blocking legitimate business emails, especially from new international partners common in UAE trade.
Ignoring Outbound Email Security
Focusing only on inbound threats while neglecting protection against compromised accounts sending malicious emails.
One-Time Configuration
Setting up security once and never reviewing or updating policies as business needs and threats evolve.
No User Training Component
Relying solely on technical controls without educating users about threat recognition and reporting procedures.
Monthly Email Security Maintenance Checklist
Note: This monthly maintenance assumes proper initial implementation and ongoing monitoring. New implementations require more intensive initial configuration and testing.
How to Choose the Right Email Security Solution for Your UAE Business
Choosing isn't about finding the "best" solution globally—it's about finding the best solution for YOUR specific situation. Here's our simple decision framework:
Our 4-Step Selection Framework
Assess Your Actual Risks
Look at your actual email traffic. Are you receiving lots of international emails? Do you handle sensitive client data? A retail business in Dubai Mall has different needs than a law firm in ADGM.
Consider Your Team's Expertise
Be honest about your internal capabilities. Some solutions need dedicated security expertise, while others are designed to be managed by your existing IT team or through a partner like us.
Evaluate Total Cost
Look beyond the subscription cost. Consider implementation time, training needs, and ongoing management. Sometimes a slightly more expensive solution saves money long-term through reduced management overhead.
Test Before Committing
Any reputable provider should offer a proof-of-concept or trial period. Test with your actual email traffic, not just demo environments.
Practical Tip from Our Experience
Start by enabling the basic email security features already available in your Microsoft 365 or Google Workspace subscription. Many businesses don't realize they already have decent protection available. Then, layer additional solutions based on your specific gaps.
Implementation Best Practices: Avoiding Common Pitfalls
We've implemented email security solutions for businesses across all seven Emirates. Here are the most common mistakes we see, and how to avoid them:
Common Mistake: Turning Everything to Maximum
Implementing all security features at maximum settings often blocks legitimate emails, especially in the UAE where business communication patterns differ from Western markets.
Our Solution: Gradual implementation with monitoring
Better Approach: Phased Rollout
Start with basic protection, monitor for a week, then enable advanced features. This approach catches threats while minimizing disruption to business operations.
Result: Better protection with fewer support calls
Our Recommended Implementation Timeline
Basic Protection & Monitoring
Enable anti-malware, anti-spam, and start monitoring traffic patterns
Advanced Threat Protection
Enable AI-based detection and BEC protection based on Week 1 data
Compliance & Encryption
Implement DLP policies and email encryption for sensitive data
Training & Optimization
Train staff and fine-tune policies based on real usage
Ready to Secure Your Business Email?
Every business we work with starts with a simple conversation about their specific needs and concerns.
For Small Businesses
Start with basic protection that grows with you
For Medium Enterprises
Comprehensive solutions with local support
For Large Corporations
Enterprise-grade protection with custom implementation
Typically respond within 15 minutes during business hours
Key Takeaways for UAE Businesses
- 1 Email security is not optional in today's UAE business environment—it's essential for both protection and compliance.
- 2 The right solution depends on your specific business needs, team capabilities, and budget—not just the "most advanced" technology.
- 3 Implementation matters as much as the technology itself. A phased approach with proper monitoring yields the best results.
- 4 Regular review and updating of your email security measures is crucial as threats continue to evolve.
At Al Hutaib, we believe that good security should protect your business without getting in the way of doing business. That's why we focus on practical, effective solutions that work specifically for the UAE market.
If you're looking for more specific guidance on implementing email security in your organization, check out our dedicated email security services page for detailed information about our approach and solutions.
Written by the Al Hutaib Security Team
With over 10 years of experience protecting UAE businesses from email threats. We combine global security expertise with local market understanding to provide practical, effective solutions.